Mule Accounts, Scam Typologies, and Real-Time Risk
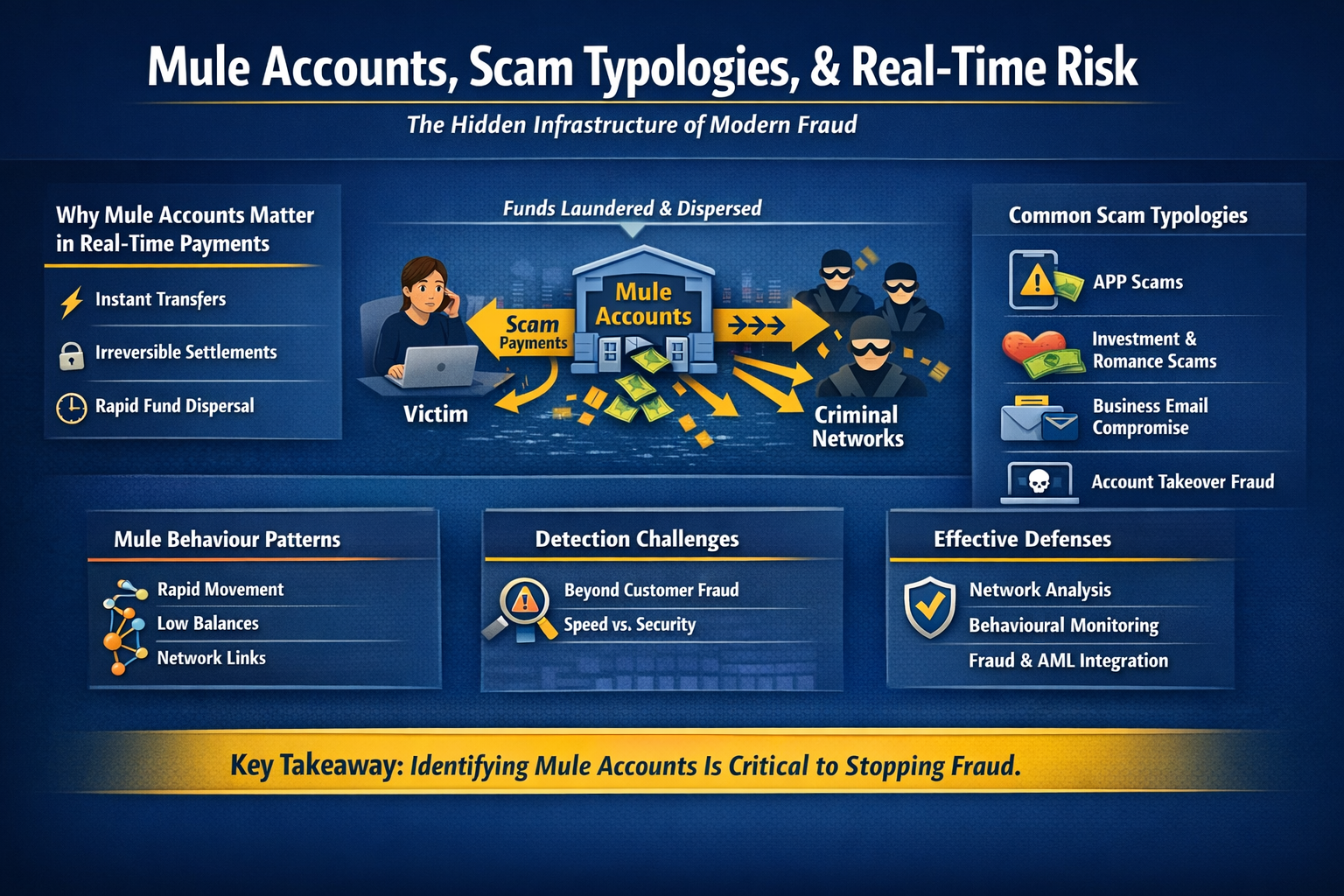
As payments move to real-time and irreversible rails, mule accounts have become the critical enabler of modern scams. While customer-facing fraud often gets the attention, it is mule networks operating behind the scenes that allow stolen funds to move, fragment, and disappear—often within minutes.
Understanding the relationship between scam typologies, mule behaviour, and real-time risk is essential for institutions seeking to protect customers and meet regulatory expectations.
Why Mule Accounts Matter More in Real-Time Payments
Mule accounts act as transit points between victims and criminal networks. In real-time environments:
- Funds are available immediately
- Settlement is irreversible
- Dispersal happens in seconds, not days
Once money enters a mule network, recovery becomes highly unlikely. Prevention must therefore focus on early identification of mule behaviour, not just customer-side fraud detection.
Common Scam Typologies Enabled by Mule Accounts
Authorised Push Payment (APP) Scams
Victims are manipulated into authorising payments to mule-controlled accounts, often under urgency or impersonation narratives.
Mule indicators
- First-time inbound payments
- Rapid outbound transfers
- Minimal account tenure
Investment and Romance Scams
Funds are transferred incrementally to build trust before larger amounts are sent and quickly laundered.
Mule indicators
- Gradual increase in inbound value
- Multiple unrelated senders
- Structured withdrawals or onward transfers
Business Email Compromise (BEC)
Invoice redirection schemes rely on mule accounts to receive corporate payments before funds are dispersed.
Mule indicators
- High-value inbound payments
- Short account dormancy followed by activity spikes
- Immediate cross-bank or cross-rail movement
Account Takeover-Driven Fraud
Compromised accounts are repurposed as mules to move funds rapidly.
Mule indicators
- Sudden behavioural change
- New payees and routing patterns
- Unusual transaction timing
Mule Behaviour Patterns in Real-Time Rails
Across typologies, mule accounts typically exhibit:
- Velocity: rapid inbound–outbound movement
- Pass-through behaviour: low balance retention
- Network connectivity: links to other risky accounts
- Operational urgency: activity clustered in short time windows
These patterns are more predictive than transaction amount alone.
Why Traditional Controls Fall Short
Legacy fraud and AML controls often struggle because they:
- Focus on post-event monitoring
- Rely on static thresholds
- Treat fraud and AML separately
- Lack network-level visibility
In real-time payments, these gaps allow mule activity to outpace detection.
Designing Controls for Real-Time Mule Risk
Network and Relationship Analysis
Controls must look beyond single transactions to:
- Counterparty relationships
- Shared attributes across accounts
- Flow-of-funds patterns
Behavioural and Velocity-Based Controls
Effective detection focuses on:
- Transaction sequencing
- Time-to-disbursement
- Deviations from normal account usage
Integration of Fraud and AML Intelligence
Mule detection sits at the intersection of fraud and AML:
- Fraud signals identify scam entry points
- AML patterns identify laundering behaviour
Leading institutions share signals across teams and systems.
Selective Intervention
Not all activity should be blocked. Controls should:
- Delay or throttle suspicious flows
- Trigger enhanced monitoring
- Escalate only when confidence is high
This protects customers without unnecessary disruption.
Operating Model Implications
Managing mule risk in real time requires:
- 24x7 monitoring and response
- Clear escalation and decision rights
- Alignment between payments, fraud, AML, and operations
- Rapid information sharing across the ecosystem
Mule risk is an ecosystem problem, not a single-institution issue.
Regulatory Expectations
Regulators increasingly expect institutions to:
- Proactively identify mule activity
- Act before funds are fully dispersed
- Demonstrate explainable decisions
- Cooperate across the payment ecosystem
Failure to manage mule risk effectively can lead to customer harm, supervisory findings, and reputational damage.
Key Takeaway
In real-time payments, mule accounts are the weak link that criminals exploit—and the control point institutions must focus on.
Institutions that design controls around behaviour, networks, and speed—rather than static rules—are far better positioned to reduce losses and protect customers in irreversible payment environments.
