Authorised Push Payment (APP) Fraud Prevention Strategies
Designing Controls for Irreversible, Customer-Authorised Payments
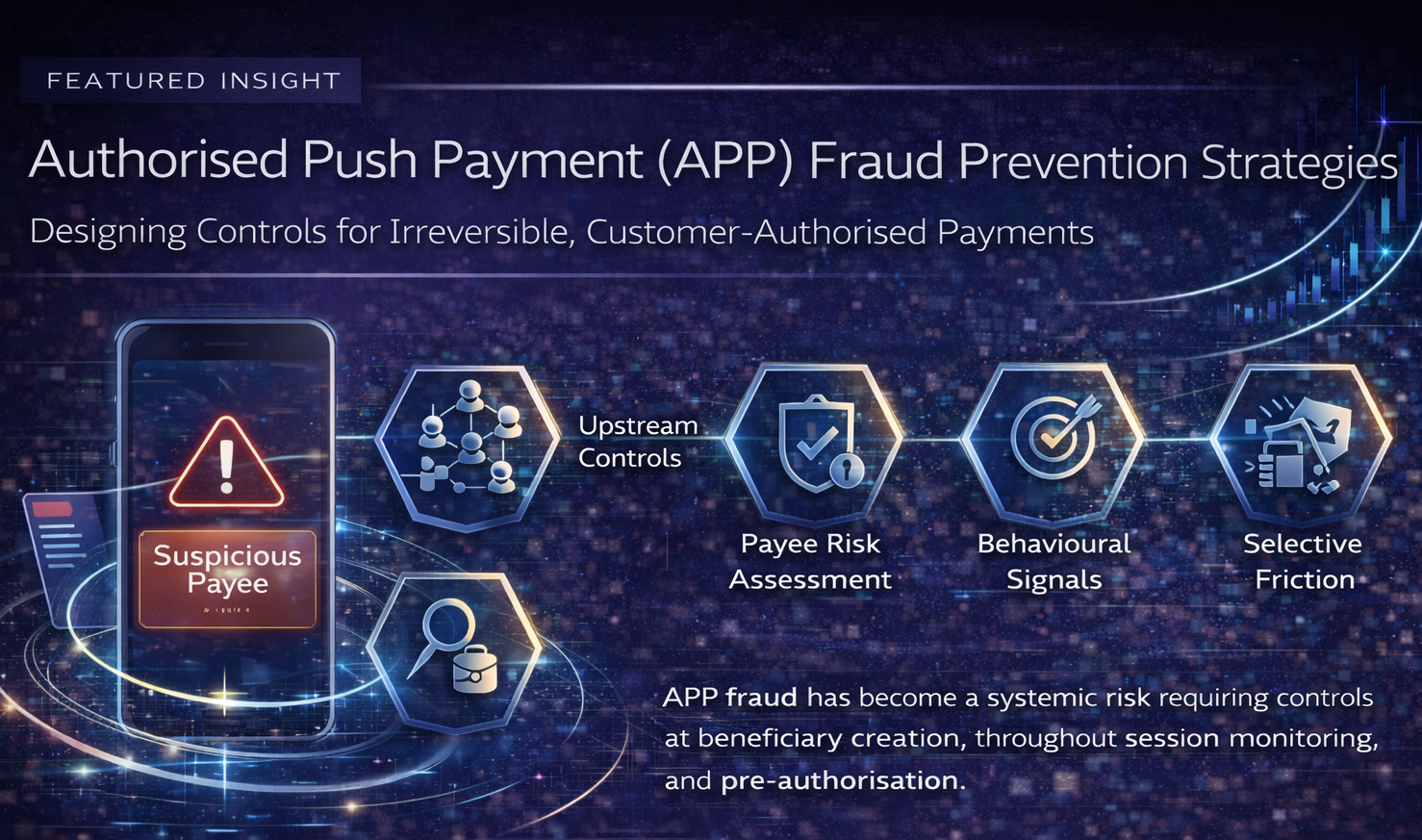
Authorised Push Payment (APP) fraud has become one of the most damaging and complex threats in modern payment systems. Customers are deceived into authorising payments themselves—often under extreme urgency or manipulation—leaving institutions with limited recovery options once funds are sent.
As instant and real-time payment rails expand, APP fraud is no longer a niche issue. It is a systemic risk that sits at the intersection of payments design, customer protection, and regulatory expectation.
Why APP Fraud Is So Hard to Stop
Unlike traditional fraud:
- The customer initiates and authorises the payment
- Authentication is technically correct
- Transactions appear legitimate at the point of execution
- Funds move instantly and irreversibly
From a systems perspective, everything looks normal—until it is too late. This makes post-event detection ineffective and places the emphasis firmly on pre-authorisation controls.
Common APP Fraud Typologies
APP fraud manifests through multiple scam narratives, including:
- Impersonation scams (banks, government, utilities)
- Investment scams
- Romance scams
- Invoice and Business Email Compromise (BEC)
- Purchase scams on digital platforms
While narratives differ, the underlying patterns are often consistent: urgency, coercion, and payment to new or mule-controlled accounts.
Core Principles for Effective APP Fraud Prevention
1. Shift Controls Upstream
APP fraud must be addressed before payment execution:
- At beneficiary creation or modification
- During customer journey and session analysis
- At the moment of payment authorisation
Controls applied after settlement are largely ineffective.
2. Focus on Payee and Mule Risk — Including Confirmation of Payee (CoP)
In APP fraud, who receives the money matters as much as who sends it.
Effective strategies assess:
- First-time or recently changed payees
- Accounts exhibiting mule-like behaviour
- Rapid inbound–outbound transaction patterns
- Network connections to known risky accounts
Confirmation of Payee (CoP) plays a critical role at this stage by:
- Comparing the payee name entered by the customer with the actual account holder name
- Flagging mismatches before payment authorisation
- Challenging scam narratives at the exact moment fraud relies on speed and trust
CoP is particularly effective against impersonation scams, where a mismatch exposes that the account does not belong to the claimed bank, government body, or utility provider.
CoP should be treated as a baseline, pre-authorisation control, not a standalone solution.
3. Use Behavioural and Contextual Signals
APP fraud often reveals itself through behavioural deviation, not transaction amount.
Key signals include:
- Unusual urgency or repeated attempts
- Deviation from normal customer payment behaviour
- Session anomalies (time of day, device changes)
- Rapid changes in payment instructions
These signals are often present even when authentication succeeds.
4. Apply Selective, Proportionate Friction
Speed is critical—but not at any cost.
Leading institutions apply:
- Contextual warnings tailored to the specific risk
- Cooling-off periods for high-risk scenarios
- Step-up authentication only when risk is elevated
Blanket friction harms customer experience and reduces effectiveness.
5. Integrate Fraud and AML Intelligence
APP fraud and money laundering are tightly linked.
Effective prevention integrates:
- Fraud indicators at payment initiation
- AML mule detection post-receipt
- Shared intelligence across teams and systems
This enables faster disruption of scam networks, not just individual transactions.
Designing Controls for Real-Time Rails
APP prevention must operate at transaction speed.
Key design elements include:
- Pre-authorisation risk scoring engines
- Tight integration with payment orchestration layers
- Real-time access to behavioural and network data
- Deterministic decision points with audit trails
Controls must be explainable immediately—to customers, operations, and regulators.
Operating Model Implications
Technology alone cannot prevent APP fraud.
Effective operating models include:
- 24x7 fraud monitoring and escalation
- Clear decision authority for delays or blocks
- Rapid customer communication and support
- Continuous tuning based on emerging typologies
APP fraud prevention is a continuous operational discipline, not a static ruleset.
Regulatory Expectations
Regulators increasingly expect institutions to:
- Proactively protect customers from authorised scams
- Demonstrate pre-authorisation controls
- Show clear decision rationale and governance
- Balance customer protection with fair access to payments
Failure to prevent foreseeable APP fraud is increasingly viewed as a control weakness, not customer error.
Common Pitfalls to Avoid
Institutions often struggle when they:
- Treat APP fraud as a customer education problem
- Rely on post-event monitoring
- Use CoP in isolation without behavioural context
- Focus only on payer-side signals
- Apply blanket friction to all customers
- Cannot explain why a payment was allowed despite warnings
These gaps frequently lead to customer harm and regulatory scrutiny.
Key Takeaway
APP fraud thrives on speed, trust, and irreversibility.
Prevention succeeds through design, timing, and integration.
Institutions that:
- Shift controls upstream
- Focus on payee and behavioural risk
- Apply selective, explainable friction
- Align technology with 24x7 operating models
are far better positioned to reduce APP fraud losses, protect customers, and meet rising regulatory expectations—without undermining the benefits of real-time payments.
